Aptean Insights
Whether you’re looking for industry insights, product details, upcoming events or our latest news it’s all right here. Browse the categories below or get in touch with one of our experts if you have a question.
Results
Showing1-15of1977
 Success Story Mar 12, 2026Heartland Produce Elevates Warehouse Efficiency With Produce Pro Software from ApteanHeartland Produce improves warehouse efficiency using Produce Pro Software from Aptean, enhancing operations, visibility, and productivity.
Success Story Mar 12, 2026Heartland Produce Elevates Warehouse Efficiency With Produce Pro Software from ApteanHeartland Produce improves warehouse efficiency using Produce Pro Software from Aptean, enhancing operations, visibility, and productivity.Read Story
 Blog Post Mar 12, 2026Comparing Food and Beverage ERP Solutions and Preparing Your Business for ImplementationWith many options to consider—from behemoth generic ERPs to niche sub-industry solutions—how do you identify the right system for your business? Find out how, now.
Blog Post Mar 12, 2026Comparing Food and Beverage ERP Solutions and Preparing Your Business for ImplementationWith many options to consider—from behemoth generic ERPs to niche sub-industry solutions—how do you identify the right system for your business? Find out how, now.Learn More
 Press Release Mar 10, 2026Aptean Launches Its Most Advanced Cloud-Native, AI-Powered Equipment Dealer Management SystemAptean launches its most advanced cloud-native, AI-powered equipment dealer management system, designed to improve efficiency, insights, and dealer operations.
Press Release Mar 10, 2026Aptean Launches Its Most Advanced Cloud-Native, AI-Powered Equipment Dealer Management SystemAptean launches its most advanced cloud-native, AI-powered equipment dealer management system, designed to improve efficiency, insights, and dealer operations.Read More
 Blog Post Feb 25, 2026Logistics Trends To Act On in 2026: What’s Shaping the Industry Right Now2026 won’t be a quiet year for logistics. From AI-driven planning to sustainable transportation and workforce change, see what you should have your eye on.
Blog Post Feb 25, 2026Logistics Trends To Act On in 2026: What’s Shaping the Industry Right Now2026 won’t be a quiet year for logistics. From AI-driven planning to sustainable transportation and workforce change, see what you should have your eye on.Learn More
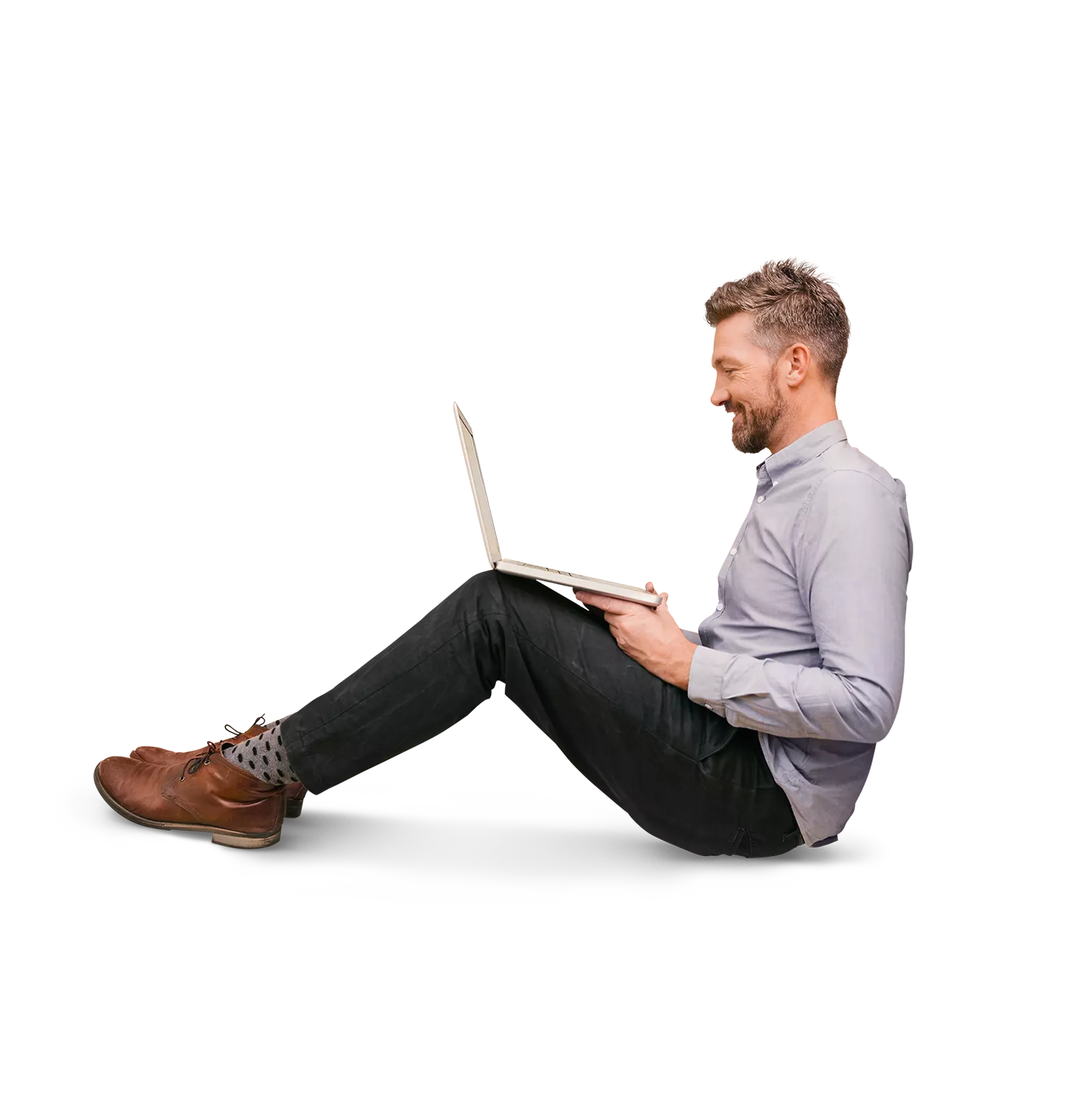
 Infographic Feb 19, 2026Aptean AppCentral Your AI Platform Purpose-Built for IndustriesAptean AppCentral is an industry-focused AI platform designed to unify systems, streamline operations, and deliver intelligent insights. Empower your business with scalable, purpose-built AI solutions.
Infographic Feb 19, 2026Aptean AppCentral Your AI Platform Purpose-Built for IndustriesAptean AppCentral is an industry-focused AI platform designed to unify systems, streamline operations, and deliver intelligent insights. Empower your business with scalable, purpose-built AI solutions.Download
 Infographic Feb 18, 2026Aptean AppCentral Your AI Platform Purpose-Built for IndustriesAptean AppCentral is an AI platform purpose-built for industry-specific needs. Connect applications, automate workflows, and drive smarter decisions with scalable, secure AI designed for your business.
Infographic Feb 18, 2026Aptean AppCentral Your AI Platform Purpose-Built for IndustriesAptean AppCentral is an AI platform purpose-built for industry-specific needs. Connect applications, automate workflows, and drive smarter decisions with scalable, secure AI designed for your business.Download
 Blog Post Feb 17, 2026Insights From Microsoft for Building High-Value, Scalable AI ProjectsEduardo Kassner shares Microsoft’s proven framework for choosing, testing and scaling AI projects that deliver real business value.
Blog Post Feb 17, 2026Insights From Microsoft for Building High-Value, Scalable AI ProjectsEduardo Kassner shares Microsoft’s proven framework for choosing, testing and scaling AI projects that deliver real business value.Learn More
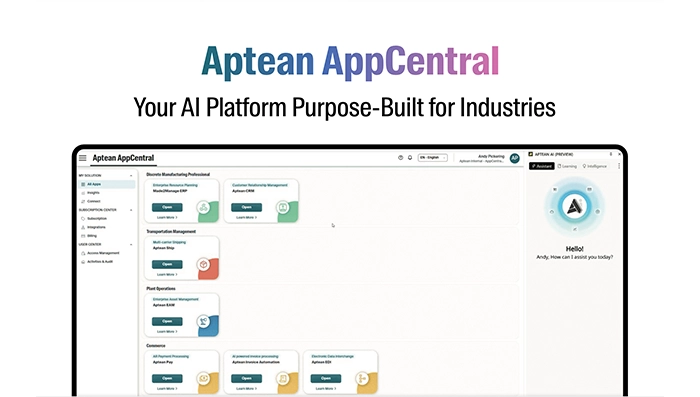
 Brochure Feb 17, 2026AppCentral Fashion & Apparel Industry Hub BrochureExplore the AppCentral Fashion & Apparel Industry Hub brochure to learn how our connected ERP platform supports apparel brands with greater visibility, efficiency, and growth.
Brochure Feb 17, 2026AppCentral Fashion & Apparel Industry Hub BrochureExplore the AppCentral Fashion & Apparel Industry Hub brochure to learn how our connected ERP platform supports apparel brands with greater visibility, efficiency, and growth.Download
 Blog Post Feb 17, 2026Do You Need Business Route Planning Software? Here's How You Can TellWhether you’re using spreadsheets or basic routing tools, here are the telltale signs that your business needs to switch to business route planning software.
Blog Post Feb 17, 2026Do You Need Business Route Planning Software? Here's How You Can TellWhether you’re using spreadsheets or basic routing tools, here are the telltale signs that your business needs to switch to business route planning software.Learn More
 Press Release Feb 17, 2026Aptean Launches the Next Generation of Fashion & Apparel Technology - AI that Puts Brands Fully in ControlAptean Launches the Next Generation of Fashion & Apparel Technology - AI that Puts Brands Fully in Control
Press Release Feb 17, 2026Aptean Launches the Next Generation of Fashion & Apparel Technology - AI that Puts Brands Fully in ControlAptean Launches the Next Generation of Fashion & Apparel Technology - AI that Puts Brands Fully in ControlRead More
 Datasheet Feb 17, 2026Designed for Fashion. Powered by AI. Built for GrowthDiscover how an AI-powered ERP platform designed for the fashion industry helps brands streamline operations, gain real-time insights, and scale confidently for growth.
Datasheet Feb 17, 2026Designed for Fashion. Powered by AI. Built for GrowthDiscover how an AI-powered ERP platform designed for the fashion industry helps brands streamline operations, gain real-time insights, and scale confidently for growth.Download
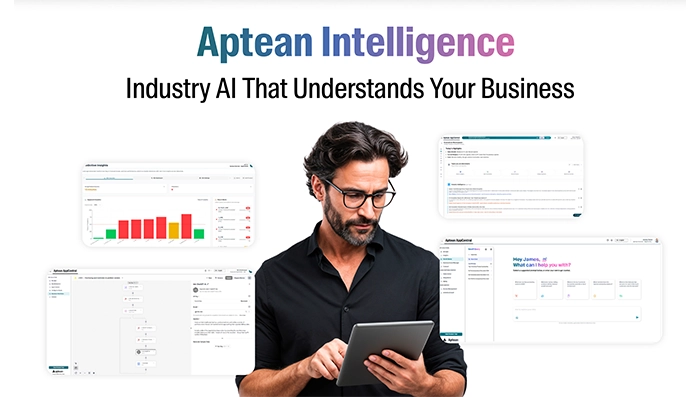 Infographic Feb 17, 2026Aptean Intelligence Industry AI That Understands Your BusinessAptean Intelligence delivers industry-specific AI built to understand your business. Unlock smarter insights, streamline operations, and drive better decisions with AI designed for your unique workflows.
Infographic Feb 17, 2026Aptean Intelligence Industry AI That Understands Your BusinessAptean Intelligence delivers industry-specific AI built to understand your business. Unlock smarter insights, streamline operations, and drive better decisions with AI designed for your unique workflows.Download
 Success Story Feb 13, 2026Spicemasters: Data Driven Control of SpicesDiscover how Spicemasters uses data to gain more control over processes, inventory, and quality, thereby increasing efficiency and supporting further growth within the spice market.
Success Story Feb 13, 2026Spicemasters: Data Driven Control of SpicesDiscover how Spicemasters uses data to gain more control over processes, inventory, and quality, thereby increasing efficiency and supporting further growth within the spice market.Read Story
 Infographic Feb 13, 2026From Bottlenecks to ROI: How Aptean TMS Transforms Shipping Into StrategyDiscover how Aptean TMS eliminates shipping bottlenecks, reduces costs and transforms transportation into a strategic driver of efficiency, visibility and measurable ROI.
Infographic Feb 13, 2026From Bottlenecks to ROI: How Aptean TMS Transforms Shipping Into StrategyDiscover how Aptean TMS eliminates shipping bottlenecks, reduces costs and transforms transportation into a strategic driver of efficiency, visibility and measurable ROI.Download
 Blog Post Feb 11, 2026The Food Industry Trends To Watch In 2026What food and beverage trends will matter most in 2026? See how consumer demand, AI and operational shifts are changing what it takes to compete.
Blog Post Feb 11, 2026The Food Industry Trends To Watch In 2026What food and beverage trends will matter most in 2026? See how consumer demand, AI and operational shifts are changing what it takes to compete.Learn More
Ready To Start Transforming Your Business?
We’ve got the specialized industry software to help your organization thrive.